Insights

Cybersecurity for SMEs in Andorra: Guide to protect your most valuable asset
In Andorra's business ecosystem, made up mainly of small and medium-sized enterprises (SMEs), a false sense of security has taken hold. Many business owners believe that, due to the size of their business or their geographic location, they are not an attractive target for cyberattacks. The reality of 2026 tells us otherwise: SMEs receive 43% of global attacks, and the consequences in Andorra can be fatal for business continuity.
Why are Andorran companies in the crosshairs?
The rapid digitalization of the Principality has created new opportunities, but also vulnerabilities. Cybercriminals use automated methods that do not distinguish between a multinational company and a local shop on Avinguda Meritxell. They look for the path of least resistance, which is often found in outdated systems or poorly trained teams.
The most common threats to local SMEs
- Ransomware: Data kidnapping that demands a financial ransom (often in cryptocurrencies) to restore access.
- Targeted phishing: Emails that impersonate Andorran banking institutions or trusted suppliers to steal credentials.
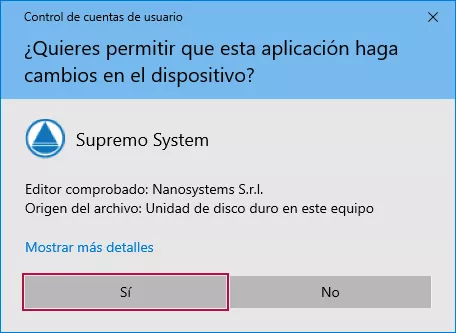
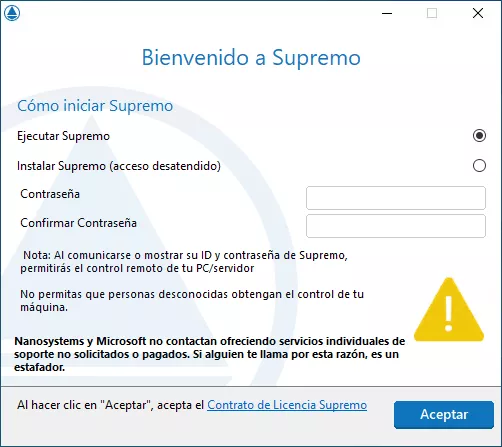
- Social engineering: Manipulation of employees to gain physical or digital access to the company’s network.
Comparison: The cost of security vs. The cost of an attack
| Concept | Investment in Prevention (Andornet) | Cost of a Cyberattack |
|---|---|---|
| Continuity | 24/7 monitoring and active systems. | Total business shutdown (average of 15 days). |
| Reputation | Full trust from your customers. | Loss of trust and potential customer churn. |
| Legality | Strict compliance with Andorra’s Data Protection Law. | Severe administrative penalties and lawsuits. |
How to implement an effective security strategy?
At Andornet, we do not believe in standard solutions. Every business requires a prior analysis. The fundamental steps are:
- Security audit: Identify where the weak points in your infrastructure are.
- Email protection: 90% of attacks enter through this channel.
- System updates: Keep software up to date to close security vulnerabilities.
- Security culture: Train your employees so they become the first line of defense.
"In Andorra, data protection is not just a technical matter; it is a pillar of our service- and trust-based economy."
Conclusion
Cybersecurity should not be a concern that keeps you awake at night, but rather a process integrated into your daily management. At Andornet, we take care of the complex part so you can focus on growing your business with complete security. We stand alongside Andorran companies to provide cutting-edge solutions and local technical support.

Frequently Asked Questions (FAQs)
1. My company is very small, do I really need a professional firewall?
Yes. Home routers do not have the capacity to detect advanced intrusions or securely manage business data traffic.
2. Does complying with Andorra’s Data Protection Law guarantee my cybersecurity?
No. The law establishes the legal framework, but cybersecurity requires technical and proactive measures to be truly effective.
3. What should I do if I believe I have been attacked?
Disconnect the device from the network immediately and contact our technical service. Do not attempt to solve it without expert supervision.